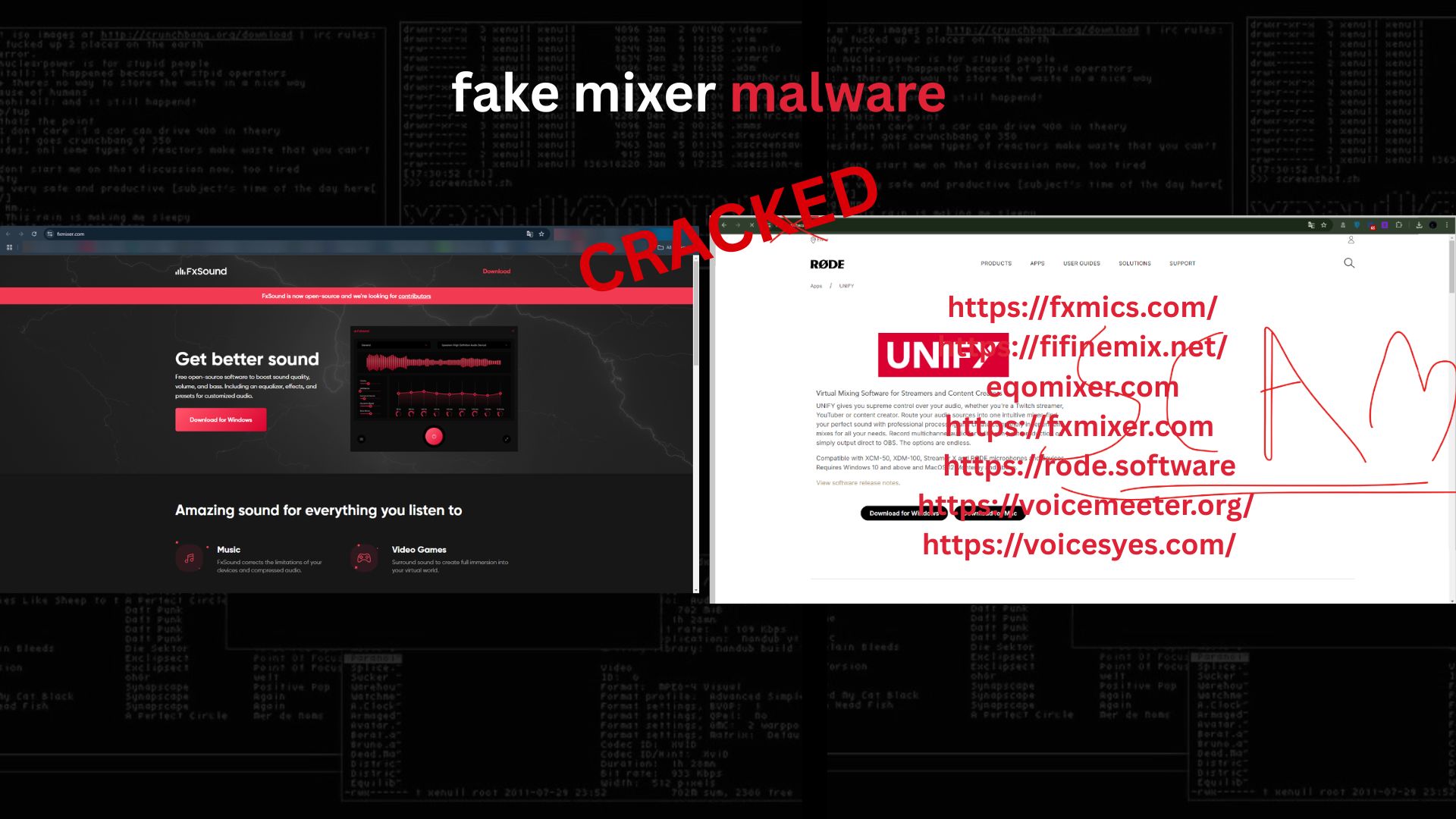
Malvertising Through “Audio Tools”: A Technical Analysis of a Stealer Campaign Delivered via Fake Voice Software
This article documents a real-world investigation into a malware distribution campaign masquerading as legitimate audio-enhancement software. The campaign leverages social engineering on Discord, professionally designed websites, and Electron-based loaders to deploy a modular information stealer. The analysis covers initial contact, infrastructure abuse, static and behavioral indicators, configuration artifacts, command-and-control (C2) logic, and underground commercialization. All sensitive actor identifiers have been intentionally redacted to comply with responsible disclosure and publication standards.