REMnux v7 [Running] - Oracle VirtualBox
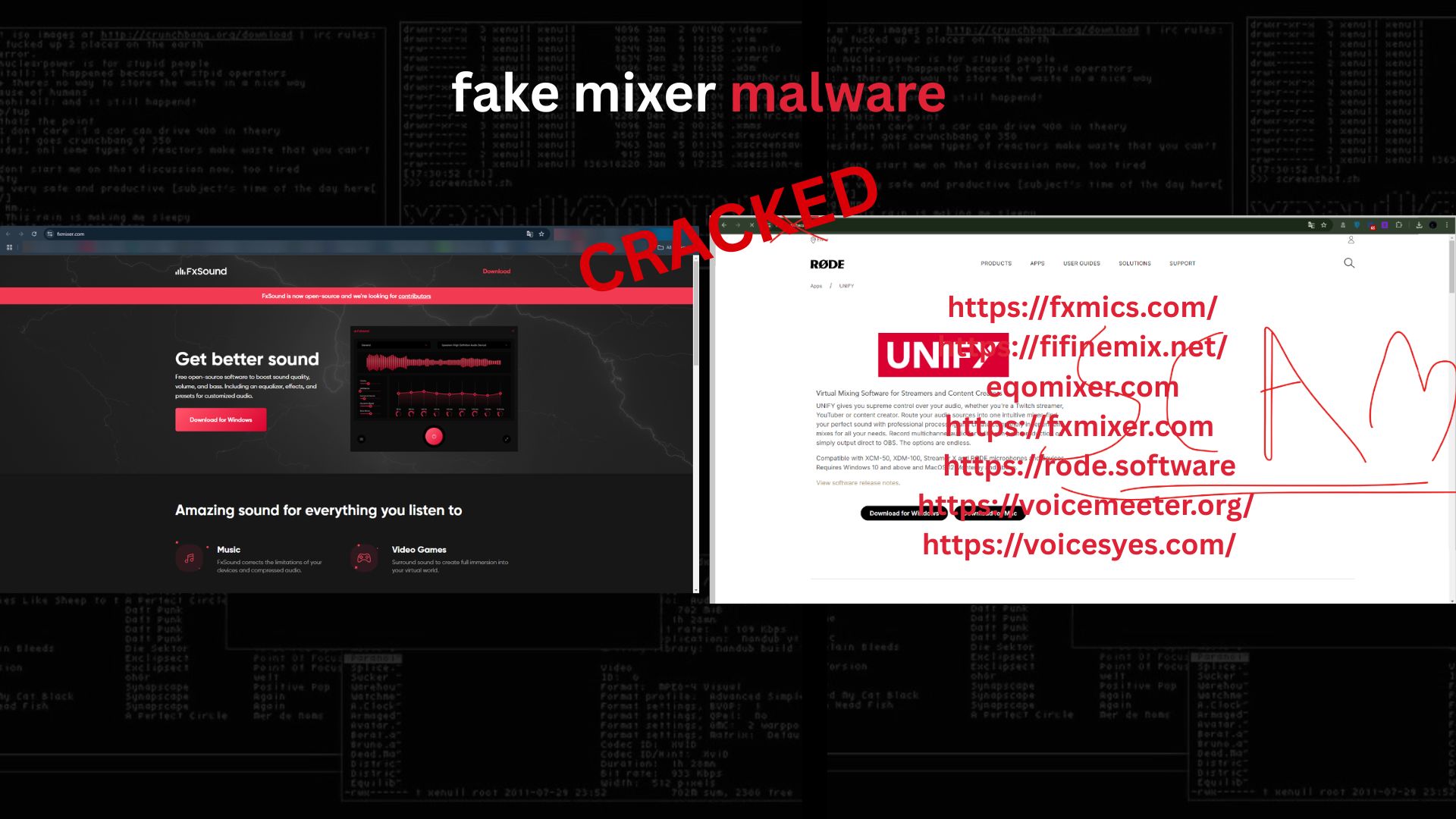
1. Initial Encounter and Social Engineering Vector
While browsing Discord, I encountered a user attempting to convince me to download a so-called “voice mixer / audio enhancer” from the website:
voicesyes[.]com
At first glance, the pitch was familiar: improved microphone quality, echo control, and “Discord-ready” enhancements. However, based on prior experience, it was immediately clear that this was not an audio tool, but rather a new camouflage technique for malware delivery.
This campaign relies on trust abuse—posing as harmless utilities commonly sought by gamers, streamers, and Discord users.
2. Trust Amplification via Fake Brand Ecosystem
To reinforce credibility, the attackers created a network of polished websites mimicking or impersonating legitimate audio brands and software ecosystems, including domains such as:
fxmics[.]com
fifinemix[.]net
eqomixer[.]com
fxmixer[.]com
rode[.]software
voicemeeter[.]org
These sites are designed to:
Appear professional and consistent
Reuse marketing language from real vendors
Funnel users toward malicious installers
Note: All listed domains were reported and taken down as part of coordinated abuse reporting.
3. Installer Analysis: Electron as a Delivery Wrapper
The downloaded sample presented itself as a Windows installer. Static inspection revealed:
NSIS-based installer
Embedded Electron application
Standard Chromium resources (V8 snapshots, pak files, locales)
app.asarcontaining obfuscated JavaScript
Electron is frequently abused in malware delivery because it:
Looks legitimate
Bundles JavaScript with native binaries
Evades naive signature-based detection
4. JavaScript Obfuscation and Loader Behavior
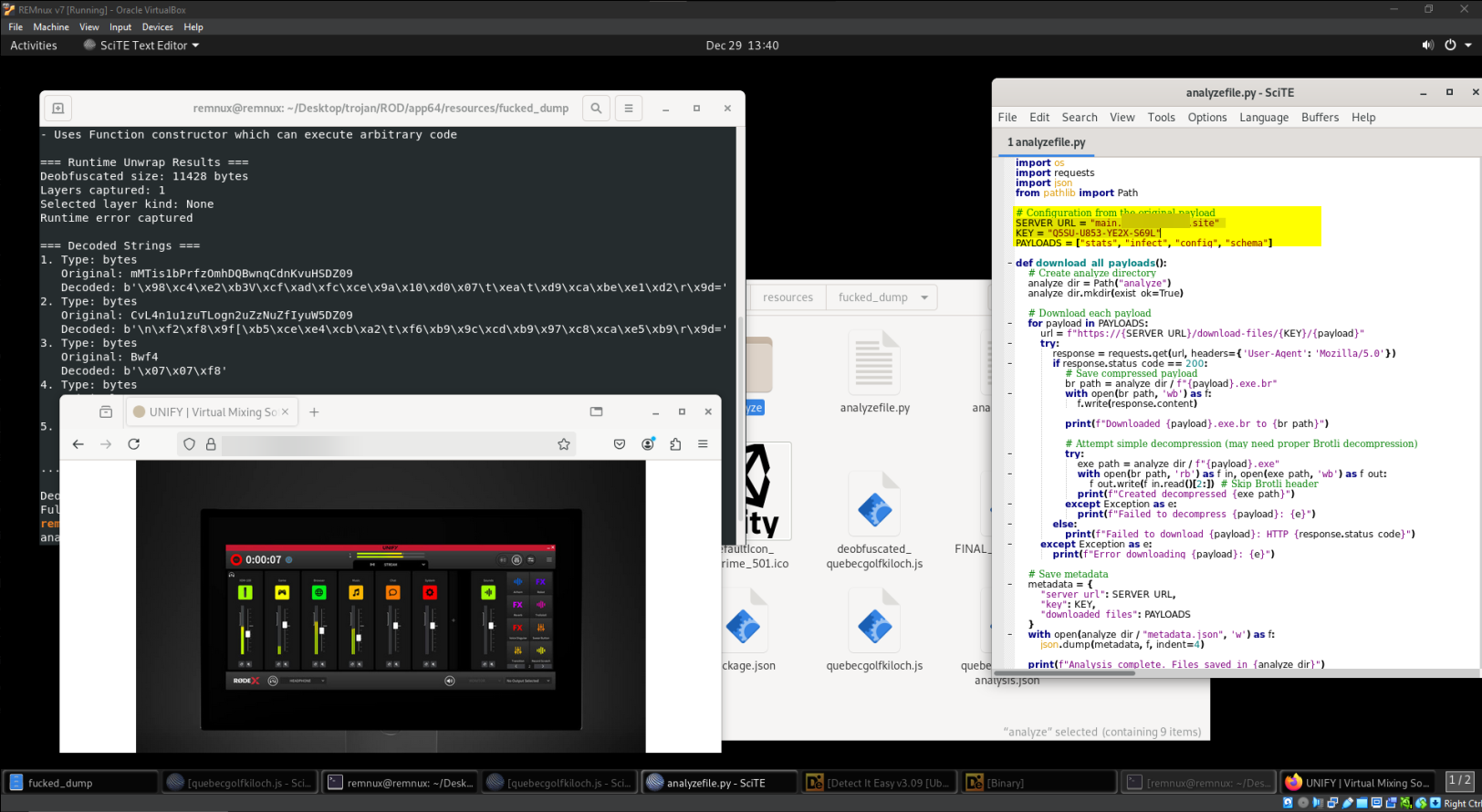
Inside the extracted app.asar, the main JavaScript file was:
Minified
Single-line
Heavily obfuscated
Using dynamic execution (
Functionconstructor)Constructing strings at runtime (
fromCharCode, encoded blobs)
Automated analysis initially failed due to intentional runtime sabotage, including undefined symbols designed to break sandboxes and emulators.
Despite this, controlled deobfuscation revealed the core purpose of the loader:
Fetch additional payloads
Decompress them in memory
Execute them silently
Maintain persistence
Bypass Windows Defender exclusions
5. Configuration Artifacts and Command Infrastructure
A recovered configuration structure revealed the operational layout:
{
"server_url": "main.[redacted].site",
"key": "Q5SU-U853-YE2X-S69L",
"downloaded_files": [
"stats",
"infect",
"config",
"schema"
]
}
Key Observations
The malware is modular
Payloads are downloaded on demand
A unique license / campaign key is used to track infections
Communication is encrypted and staged
6. Payload Roles (High-Level)
Without executing any malicious code, static correlation indicates:
stats → System and user data collection
infect → Secondary infection or injection logic
config → Persistence and startup mechanisms
schema → Data packaging and exfiltration preparation
Execution is hidden using:
VBS wrappers
wscript.exe/cscript.exeBackground execution flags
Randomized directories in
AppData
7. Discovery of the Commercial Backend
Further investigation into the recovered configuration data led to the discovery of a publicly advertised stealer service, hereafter referred to as “the project” (name intentionally withheld).
Marketing material associated with the service offered:
White-Label Packages
Full setup with continuous support
Monthly infrastructure fees
Reseller model (profit retention by buyer)
Optional source code access at higher cost
License-Based Access
Short-term and long-term licenses
Tiered pricing
Subscription-style expiration
Payment Methods
Cryptocurrency
This confirms the malware is not a one-off attack, but a commercial Malware-as-a-Service (MaaS) operation.
8. Validation via Bot Interaction (Evidence of Active Infrastructure)
Using the recovered campaign key, interaction with the project’s automated control bot returned valid responses, including:
Command listings
License status
Expiration timestamps
The bot confirmed the key was:
Actively registered
Time-limited
Recognized by backend systems
This conclusively proves that:
The infrastructure is live
The malware is operational
The analysis correlates with real attacker tooling
🔑 Key: Q5SU-U853-YE2X-S69L
📅 Created at: Mon Dec 22 2025 15:23:51 GMT+0000 (Greenwich Mean Time)
⏱ Time remaining: 54d 19h 9m 27s
9. Indicators of Compromise (Redacted)
To prevent abuse replication, indicators are partially redacted:
C2 domain:
main.[redacted].siteElectron loader with obfuscated JS
NSIS installer embedding Chromium resources
Use of Defender exclusion commands
Persistence via Startup VBS scripts
Discord-based data exfiltration (webhooks embedded in secondary payloads)
All relevant indicators were submitted to:
Hosting providers
Platform abuse teams
Security reporting channels
10. Conclusion
This investigation demonstrates how modern malware campaigns:
Exploit user trust on social platforms
Abuse Electron for stealthy delivery
Operate as commercial products
Scale via white-label distribution
Target non-technical users through familiar “utility” lures
The case highlights the importance of:
Verifying software sources
Treating “free tools” with skepticism
Monitoring Electron-based installers
Rapid reporting of malicious infrastructure
What initially appeared to be a harmless audio utility was, in reality, a fully monetized information-stealing operation with professional support, licensing, and active customer onboarding.
Dis
This article is published strictly for educational, defensive, and awareness purposes.
Comments
No comments yet. Be the first to comment!